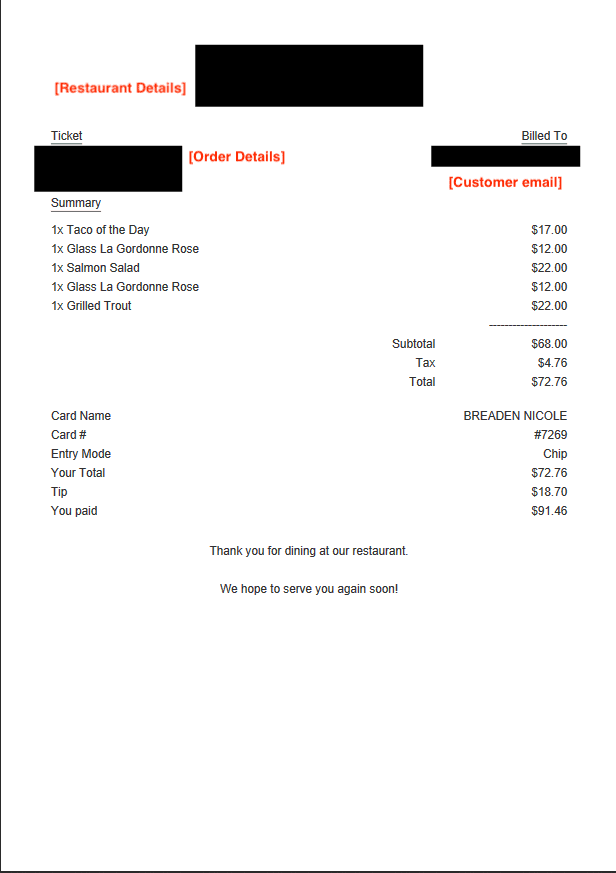
According to cybersecurity company vpnMentor, the database was brought to its attention via Helen Foster, a partner at Davis Wright Tremain, who shared the findings exclusively with TNW. PayMyTab — an at-table payment system — is a mobile app and device that enables diners to settle their checks using their secure EMV chip-enabled credit card. It also enables guests to split the bill and pay it, tip included, directly from their own phones. The leaked personal information included the following details:
Customer’s name Email address or cell telephone number Last 4 digits of the payment card number The meal items ordered The date, time, location, and the name of the restaurant visited
As a result, any customer who used PayMyTab to pay for their meals between July 2, 2018 to early November of this year could have had the aforementioned details exposed this way. We’ve reached out to PayMyTab for further details, and we’ll update the story if we hear back. “The S3 bucket contained detailed records of any customer at a restaurant using PayMyTab, who had chosen to have their receipt emailed to them after a meal,” vpnMentor stated. “By providing their email address, they could view their receipt online from their email inbox.” While the database storage bucket may have been secured now, the possibility that criminals could use the exposed customer information to stage a variety of spearphishing attacks still remains. This is not the first time that vpnMentor has discovered databases and servers left wide-open to the public. The company has previously disclosed a massive data breach impacting Ecuadorian citizens, Chinese e-commerce firm Gearbest, and a hotel reservation system used by resorts to manage web bookings. It goes without saying that database leaks of this kind have huge security ramifications, including providing hackers easy access to sensitive information, thereby serving as a springboard for mounting other kinds of phishing exploits. Therefore, it’s crucial that you watch out for any suspcious emails, enable two-factor authentication, and not click any links that could trick you into revealing private or sensitive information.